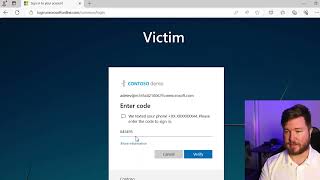
Media Summary: Adversary-in-the-Middle (AitM) attacks are one of the most dangerous ways threat actors Resources: Enroll in my Courses (search for Tyler Ramsbey) Support me on Ko-Fi ... Did you know that entering your credentials on a phishing website can compromise your account—even if you have
How Attackers Bypass Mfa Multi Factor Authentication Security Simplified - Detailed Analysis & Overview
Adversary-in-the-Middle (AitM) attacks are one of the most dangerous ways threat actors Resources: Enroll in my Courses (search for Tyler Ramsbey) Support me on Ko-Fi ... Did you know that entering your credentials on a phishing website can compromise your account—even if you have Thank you to ThreatLocker for sponsoring my trip to ZTW26 and also for sponsoring this video. To start your free trial with ... Learn Web App Pentesting for free, right in your browser ⏱️ Only 3 hours 🛠️ No VMs, no setup ... Membership // Want to learn all about cyber-
PlexTrac makes pentest reporting a breeze -- try their premiere reporting & collaborative platform: ... Discover how to safeguard your accounts against
















![How Hackers Bypass MFA? [2 Ways To Stop Them]](https://i.ytimg.com/vi/NsdkxvSSRoo/mqdefault.jpg)