Media Summary: In this video, we delve into the tactics employed by Phishing attacks are evolving, and even multi-factor authentication ( Still using SMS text codes for 2-Step Verification? You might be at risk. In this video, I break down exactly why
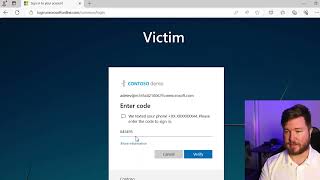
Mfa Bypass How Hackers Exploit And Bypass It - Detailed Analysis & Overview
In this video, we delve into the tactics employed by Phishing attacks are evolving, and even multi-factor authentication ( Still using SMS text codes for 2-Step Verification? You might be at risk. In this video, I break down exactly why 2FA is supposed to be your last line of defense. But what if it's not as unbreakable as you think? This video is for educational and ... Thank you to ThreatLocker for sponsoring my trip to ZTW26 and also for sponsoring this video. To start your free trial with ... FREE Cybersecurity Training: Full Cybersecurity Short ...
Two-factor authentication is one of the best things you can implement on your online accounts to keep them secure. But Resources: Enroll in my Courses (search for Tyler Ramsbey) Support me on Ko-Fi ... The Cyber Pro Podcast: Trevor Hilligoss – The Truth About CRITICAL SECURITY WARNING: Cybercriminals have discovered sophisticated methods to Learn how the Browser in the Browser attack is used by