Media Summary: This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... This video tutorial has been taken from Hands-On Penetration Testing with In this video i will be showing you how to gain a root shell by exploiting the
Beginning Metasploit Scanning Ftp Services Packtpub Com - Detailed Analysis & Overview
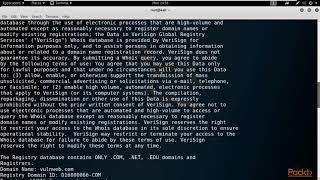
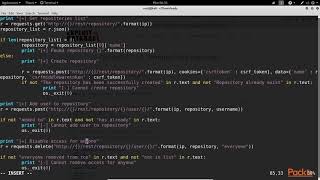
This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... This video tutorial has been taken from Hands-On Penetration Testing with In this video i will be showing you how to gain a root shell by exploiting the In this video, we explore how to exploit the 126 Metasploit Scanner Modules Demonstration This video tutorial has been taken from Practical Windows Penetration Testing. You can learn more and buy the full video course ...
Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ... Every successful network compromise — from the smallest ransomware incident to the largest nation-state breach —