Media Summary: This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... This video tutorial has been taken from Hands-On Penetration Testing with This video tutorial has been taken from Practical Windows Penetration Testing. You can learn more and buy the full video course ...
Finding And Exploiting Hidden Vulnerabilities Setting Up Metasploit Packtpub Com - Detailed Analysis & Overview
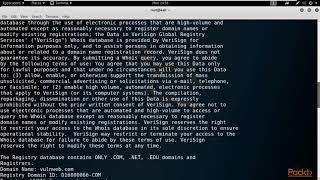
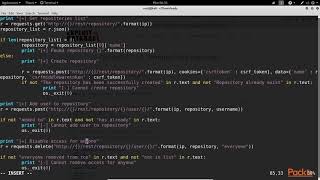
This playlist/video has been uploaded for Marketing purposes and contains only selective videos. For the entire video course and ... This video tutorial has been taken from Hands-On Penetration Testing with This video tutorial has been taken from Practical Windows Penetration Testing. You can learn more and buy the full video course ... Part of 'Kali Linux - Backtrack Evolved: Assuring Security by Penetration Testing' video series. For the full Course visit: ... Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: Join Rob Fuller on this ethical When used correctly, it is a great asset to a ballpoint tester, but it does have its drawbacks..
This video tutorial has been taken from Learning










![Using Metasploit Capture Modules - Metasploit Minute [Cyber Security Education]](https://i.ytimg.com/vi/H_E3FNF8rBw/mqdefault.jpg)




