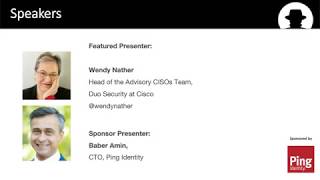
Media Summary: Learn about current threats: Learn about IBM Listen in as our Sr. Director of IT Risk and Security discusses how we use Akamai enterprise security products to protect our ... By Wendy Nather, Head of Advisory CISOs Team, Duo Security at CISCO and Baber Amin, Ping Identity CTO In this session, learn ...
Zero Trust The Typical Company Journey - Detailed Analysis & Overview
Learn about current threats: Learn about IBM Listen in as our Sr. Director of IT Risk and Security discusses how we use Akamai enterprise security products to protect our ... By Wendy Nather, Head of Advisory CISOs Team, Duo Security at CISCO and Baber Amin, Ping Identity CTO In this session, learn ... Meet Dave, the leader of a large, complex organization responsible for deciding whether to accept, avoid, transfer, or mitigate their ... Security+ Training Course Index: Professor Messer's Course Notes: ... Modern Work & Security expert, Hector Perez, explains what
In a world where bad actors exploit data,