Media Summary: By the end of this video, you'll have a solid understanding of how This video is part of the Udacity course "Intro to Information Help Support the Channel by Donating Crypto ₿ Monero ...
Security Of Rsa Applied Cryptography - Detailed Analysis & Overview
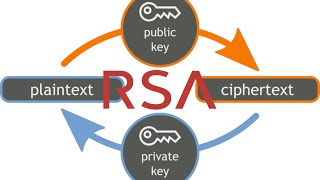
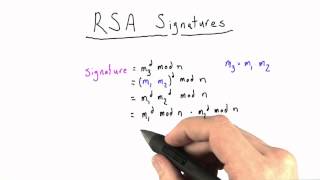
By the end of this video, you'll have a solid understanding of how This video is part of the Udacity course "Intro to Information Help Support the Channel by Donating Crypto ₿ Monero ... Learn about prime factor and public-key selection as well as benefits and pitfalls of The RSA Encryption Algorithm (1 of 2: Computing an Example) Oxford Sedleian Professor of Natural Philosophy Jon Keating explains the