Media Summary: This module covers the difference between the block modes noted in the title, from Domain 3, Security Architecture and ... You don't just 'run a cipher' - you need a mode of operation. Dr Mike Pound explains some relative to the Feistel cipher. **This ... CISSP Domain 3 Cryptographic Cipher Modes of Operation: 0:00 Crypto Pizza Analogy Intro (Plaintext vs Ciphertext) 1:01 Stream ...
Ecb Cbc Cfb Ofb Ctr - Detailed Analysis & Overview
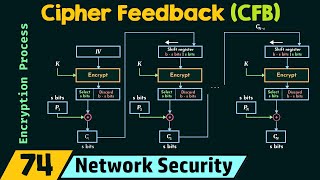
This module covers the difference between the block modes noted in the title, from Domain 3, Security Architecture and ... You don't just 'run a cipher' - you need a mode of operation. Dr Mike Pound explains some relative to the Feistel cipher. **This ... CISSP Domain 3 Cryptographic Cipher Modes of Operation: 0:00 Crypto Pizza Analogy Intro (Plaintext vs Ciphertext) 1:01 Stream ... 1. Electronic Code Book Mode 2. Cipher Block Chaining Mode 3. Output Feedback Mode 4. Cipher Feedback Mode 5. Counter ... Network Security: Block Cipher Modes of Operation Topics discussed: 1. Need for having Block Cipher Modes of Operation. 2. In this video, we break down the essential concepts behind block cipher modes of operation and how they secure modern ...
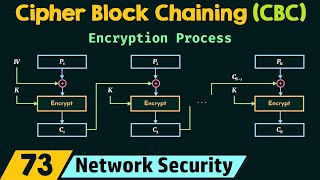
Network Security: Cipher Block Chaining ( AES encryption ECB CBC CFB OFB CTR GCM شرح Cipher modes of operation define how block ciphers like AES and DES encrypt data securely. In this video, we explain the most ... كورس امن المعلومات شرح Mode Operation - We have 5 Modes of operation. 1. Electronic code book 2. cipher block chaining 3.cipher feedback mode 4. output feedback mode ... If you like IQPOP please SHARE, LIKE COMMENT, AND SUBSCRIBE to this CHANNEL. Electronic Codebook Book (
Security+ Training Course Index: Professor Messer's Course Notes: ... Is your encryption leaking secrets? 🕵️♂️ It's not enough to have a strong lock; you need a master plan for how to use it. You can buy me a coffee if you want to support the channel: I explain all six modes of ...