Media Summary: A comprehensive step by step beginner's guide to Learn Earn $$. Learn What You Need to Get Certified (90% Off): Three Ways Hackers Can Hack into Welcome to Day 26 of the 30-Day MyDFIR SOC Analyst Challenge! This challenge is designed to help aspiring SOC Analysts like ...
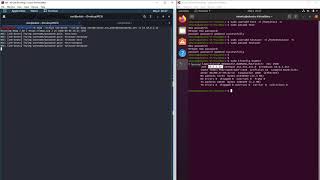
Brute Force Attack Test On Ssh Sever - Detailed Analysis & Overview
A comprehensive step by step beginner's guide to Learn Earn $$. Learn What You Need to Get Certified (90% Off): Three Ways Hackers Can Hack into Welcome to Day 26 of the 30-Day MyDFIR SOC Analyst Challenge! This challenge is designed to help aspiring SOC Analysts like ... Using a list of possible passwords to try to get into an Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ... Ever wondered how attackers discover weak passwords on
Learn the basics of Offensive Cybersecurity in our five-day hands-on course- Visit website ... This is a great simple tutorial on how to Solution by Mads Frandsen. MCSI's Online Learning Platform provides uniquely designed exercises for you to acquire in-depth ...