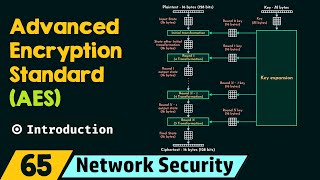
Media Summary: In 1997, a contest began to develop a new encryption algorithm to become the Your browser is using this system right now! (at time of typing!) - Dr Mike Pound explains this ubiquitous system! EXTRA BITS with ... Interested in studying cybersecurity at the highest level? Bochum offers one of the most
Aes Explained Advanced Encryption Standard Computerphile - Detailed Analysis & Overview
In 1997, a contest began to develop a new encryption algorithm to become the Your browser is using this system right now! (at time of typing!) - Dr Mike Pound explains this ubiquitous system! EXTRA BITS with ... Interested in studying cybersecurity at the highest level? Bochum offers one of the most This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... UPDATE: The Flash app got rewritten in HTML5! Now it is interactive again, and you can click through it in your own pace: ... How do you verify that someone is who they say they are? Dr Mike Pound on digital signatures.
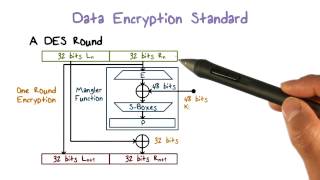
Substitution-permutation networks are the basis for almost all modern symmetric This video is part of an online course, Applied