Media Summary: So in this second part of the video we're going to look at a little bit of background on on This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... By the end of this video, you'll have a solid understanding of how RSA works, from key generation to encryption and decryption, ...
5 4 Confidentiality Modular Arithmetic And Oaep - Detailed Analysis & Overview
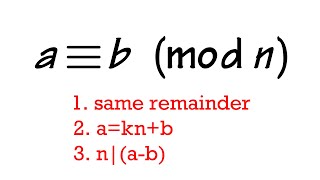
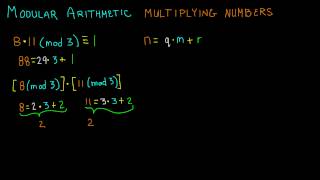
So in this second part of the video we're going to look at a little bit of background on on This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... By the end of this video, you'll have a solid understanding of how RSA works, from key generation to encryption and decryption, ... Interested in studying cybersecurity at the highest level? Bochum offers one of the most advanced academic environments for ... In this tutorial, I demonstrate two different approaches to multiplying numbers in Sign up with brilliant and get 20% off your annual subscription: STEMerch Store: ...
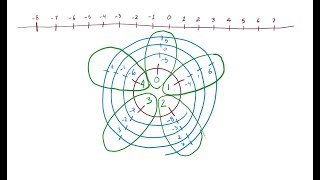
Question 6 from Tom Rocks Maths and I Love This is the sixth video in a series of videos that leads up to the Sign up for Number Theory course (coming soon) on our website: MIT 18.200 Principles of Discrete Applied