Media Summary: The "fortress" model of cybersecurity is officially crumbling. For decades, businesses relied on a strong perimeter—think of it ... Enterprise IT has changed more in the last decade than in the previous three. From data centers to STOP BUYING "ZERO TRUST." Most vendors want to sell you a VPN replacement and call it Zero Trust, but as an architect, you ...
Invisible Infrastructure The Dark Cloud Strategy For Security - Detailed Analysis & Overview
The "fortress" model of cybersecurity is officially crumbling. For decades, businesses relied on a strong perimeter—think of it ... Enterprise IT has changed more in the last decade than in the previous three. From data centers to STOP BUYING "ZERO TRUST." Most vendors want to sell you a VPN replacement and call it Zero Trust, but as an architect, you ... Your Linux servers aren't just running containers anymore—they're hosting Join us for a power-packed 30-minute webinar where Alex Cooley and Cameron Laughlin, ATC Delta Team Consultants, discuss ... In this episode of On Target with Archer, Stacy Bresler breaks down the role of data diodes in network segmentation for critical ...
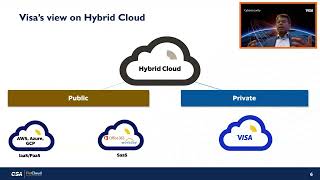
Josh Stella, CEO and Co-Founder of Fugue, will walk through a Subra Kumaraswamy, CISO of Visa, will take to the main stage to deliver his unique experience managing cyber risk in the ... Join us for an insightful Q&A session where our experts delve into the